Fraud
Apply for the 2026 SRIFCU Memorial Scholarship
At SRI Federal Credit Union, we believe in investing in our members, not just financially, but in their futures. That’s why we are proud to announce that we are now accepting applications for our 2026 SRIFCU Official Memorial Scholarship.
Each year, this scholarship program honors the legacy of past credit union volunteer officials whose dedication helped shape the strong, member-focused institution we are today. Through this program, we aim to support the next generation of students as they take the next step in their educational journey. SRI Federal Credit Union will award up to four (4) scholarships, each valued at $1,500, to eligible students pursuing higher education. These scholarships are awarded in honor of past volunteer officials, including: Their commitment to service and community continues to inspire us, and this scholarship is one way we carry that legacy forward. Applicants must meet the following criteria: We encourage all eligible students to apply early and ensure all required documentation is submitted before the deadline. Students can complete and submit their application HERE. Be sure to review all eligibility requirements and include any necessary supporting materials to ensure your application is considered. The SRIFCU Memorial Scholarship is more than just financial assistance, it’s an opportunity to be recognized by your credit union for your hard work, goals, and commitment to your future. Whether you’re planning to attend a university, pursue a trade, or continue your education at a higher level, this scholarship can help ease the financial burden and allow you to focus on what matters most: your success. At SRI Federal Credit Union, our mission has always been rooted in supporting our members at every stage of life. From your first savings account to major life milestones like education and homeownership, we’re here to help you succeed. We are honored to support students in our community and look forward to reviewing this year’s applications. As scholarship opportunities become more visible this time of year, so do scams. Keep these tips in mind: If you ever have questions, feel free to contact us directly, we’re here to help. Don’t miss your chance to be considered for the 2026 SRIFCU Memorial Scholarship. We wish all applicants the very best of luck and look forward to supporting your educational journey.
Scholarship Details
Who Is Eligible to Apply?
Important Dates
How to Apply
Why Apply?
Investing in Our Members’ Future
A Quick Reminder: Stay Safe from Scholarship Scams
Apply Today
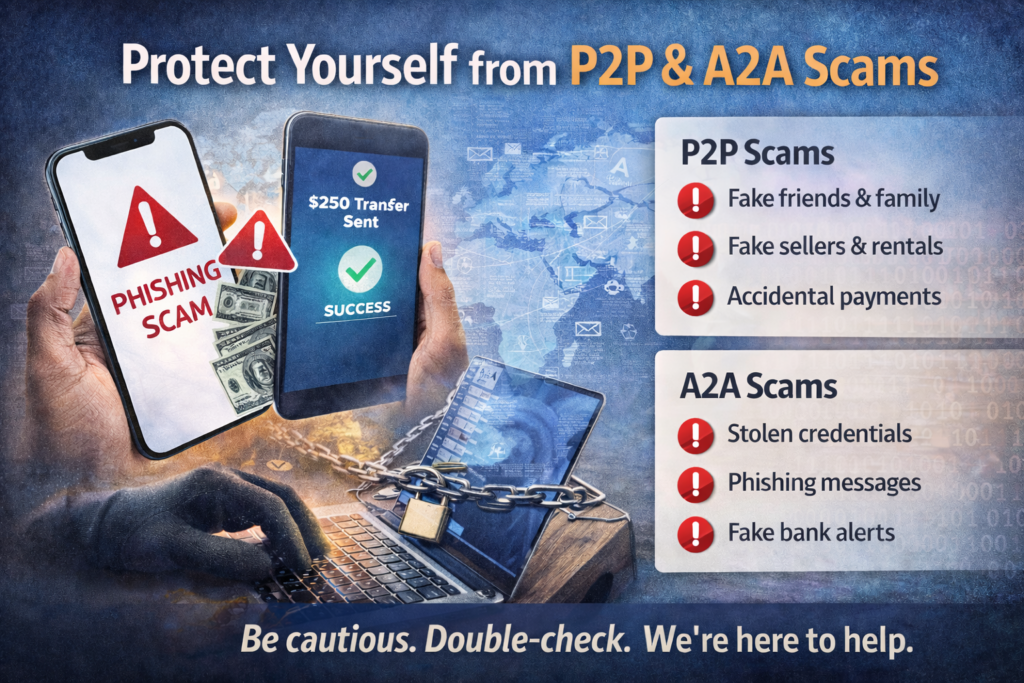
P2P & A2A Fraud: What It Is, How It Happens, and How to Stay Safe
Sending money digitally is fast and convenient. Whether you’re paying a friend back for dinner or transferring money between accounts, tools like person-to-person (P2P) payments and account-to-account (A2A) transfers make life easier. Unfortunately, scammers know this, and they’re taking advantage. At SRI Federal Credit Union, we want to help you understand how these scams work and what you can do to protect yourself. P2P fraud happens when someone tricks you into sending them money directly. Because these payments are quick and usually final, it can be hard to get funds back once they’re sent. Common P2P scams include: Someone pretending to be a friend or family member asking for money urgently Fake sellers or rentals that disappear after payment “Accidental payment” scams, where someone asks you to send money back Fake tech or banking support asking you to “verify” your account with a payment If the request feels rushed or unusual, that’s a big red flag. A2A fraud involves unauthorized transfers between bank accounts. These scams often start with stolen login information or convincing messages that look legitimate. Common A2A scams include: Phishing emails or texts that steal your online banking login Fake invoices or payment requests Scammers posing as employers, vendors, or financial institutions Account takeovers after credentials are compromised Most scams rely on pressure and emotion. Fraudsters often: Create urgency (“Act now!”) Pretend to be someone you trust Use fear or authority to rush you into action Taking a moment to pause and double-check can stop a scam in its tracks. Quick safety tips: Only send money to people you know and trust Never share passwords or one-time passcodes Be cautious with urgent payment requests Double-check unexpected messages, even if they look familiar Review your account activity regularly Act fast: Contact SRI Federal Credit Union right away Stop any pending transactions if possible Change your passwords Report the scam so we can help protect others Scammers are always changing tactics, but staying informed makes a big difference. If something feels off, trust your instincts and reach out. We’re here to help keep your money safe.
What Is P2P Fraud?
What Is A2A Fraud?
Why Scammers Are Successful
How You Can Protect Yourself
Think You’ve Been Targeted?
We’ve Got Your Back
New California Law Helps Protect Seniors from Financial Scams
Beginning January 1, 2026, California’s new law (SB 278) strengthens protections for seniors against financial scams and exploitation. At SRI Federal Credit Union, we believe in protecting our members, which is why we are implementing these protections ahead of the official effective date. This law, championed by Bill Dodd, is designed to help prevent elder financial abuse by creating an extra layer of security and support. What Is SB 278? SB 278 requires financial institutions to maintain an Emergency Financial Contact Program for members ages 65 and older. This allows members to name a trusted contact who we can notify if suspected abuse or unusual activity occurs during employee-assisted transactions. At SRI Federal Credit Union, we are adopting these protections early to help keep our senior members safer, sooner. How Our Early Program Works To make enrollment easy, we will include a Trusted Contact Authorization Form inside the 2025 year-end account statements. With this form, members can: If you would like to complete the form before receiving your year-end statement, simply contact us, and we will be happy to send it to you. Key Protections You Can Expect As part of this program, we may: These protections mainly apply to employee-assisted transactions, such as teller withdrawals and in-branch transfers. What This Means for Seniors If you are 65 or older, you may notice: These safeguards are designed to protect you, not to slow down legitimate access to your funds. Our Commitment to You At SRI Federal Credit Union, your safety comes first. Implementing these protections early reflects our commitment to helping prevent fraud and protect the financial well-being of our members. If you have questions or would like a Trusted Contact Authorization Form sent to you before your statement arrives, please contact us.
Amazon Issues Urgent Alert: 300 Million Customers at Risk Amid Holiday Cyberattacks
As the 2025 holiday shopping season hits full stride, Amazon is warning all 300+ million of its customers to stay on high alert. With Black Friday sales stretching longer each year, cybercriminals are exploiting the shopping surge, and new data shows their tactics are more aggressive and convincing than ever.
Why Amazon Is Sounding the Alarm
In a November 24 email sent to users, Amazon warned that scammers are increasingly impersonating the company to steal sensitive personal and financial information. These attacks aren’t new, but they’re evolving fast, especially with artificial intelligence making fake messages, spoofed websites, and fraudulent alerts look more realistic.
According to Amazon, attackers are reaching out using:
- Fake delivery or “account issue” notifications
- Social media ads for unreal “too-good-to-be-true” deals
- Messages from unofficial channels asking for login or payment info
- Suspicious or unfamiliar links
- Unsolicited tech support phone calls
Amazon stresses that customers should treat any unexpected message requesting credentials or payment information with extreme caution.
New Report Confirms Rising Holiday-Themed Scams
A fresh FortiGuard Labs report backs up Amazon’s warning. The findings reveal:
- 18,000+ holiday-themed domains registered in the last three months
- 750 confirmed malicious
- 19,000+ domains impersonating major brands, including Amazon
- 2,900 malicious brand lookalike domains
Cybercriminals are crafting domains with slight variations, easy to miss during the rush of holiday shopping. Experts warn that AI is accelerating the sophistication of these scams, making fake order confirmations, spoofed retailer websites, and forged customer service interactions more convincing than ever.
The FBI Confirms Massive Financial Damage
In a new public service announcement on November 25, the FBI warned that brand impersonation attacks are fueling a surge in account takeovers. Since January 2025, thousands of victims have reported losses totaling more than $262 million.
These scams often involve:
- Phone, text, email, or instant message contact from someone pretending to be customer support
- Claims of “fraudulent activity”
- A link to a realistic but fake website
- Victims entering their login, MFA code, or one-time passcode
- The attacker using those credentials to reset the password and take over the account entirely
Although the FBI’s alert focuses on financial institutions, the tactics apply to all major brands, including Amazon.
How Amazon Says You Can Protect Yourself
Amazon is urging customers to take the following steps to protect their accounts year-round:
1. Use Only Official Amazon Channels
Rely exclusively on the Amazon app or amazon.com for customer service, order tracking, refunds, and account updates.
2. Enable Two-Factor Authentication (2FA)
2FA adds a crucial layer of protection against unauthorized access.
3. Use Passkeys
Passkeys let you sign in using biometrics (face, fingerprint) or your device PIN, a safer alternative to passwords.
4. Remember What Amazon Will Never Do
Amazon will never:
- Ask for payment over the phone
- Request payment information via email
- Ask you to verify account credentials through links or messages
If you receive messages asking for any of those, assume it’s fraudulent.
Stay Vigilant This Holiday Season
With AI-powered scams accelerating and brand impersonation attacks spiking, Amazon’s warning is timely and necessary. Whether you’re shopping for holiday deals or simply checking order updates, a moment of caution could save you from a costly scam.
Stay safe and always confirm before you click.
Beware of Bitcoin ATM Scams: What You Need to Know to Stay Safe
As technology evolves, so do the ways scammers try to take advantage of unsuspecting victims. One of the latest tactics involves Bitcoin ATMs—machines that let users buy cryptocurrency using cash or debit cards. While legitimate Bitcoin ATMs exist, scammers have found ways to exploit them to steal money from innocent people. At SRI Federal Credit Union, protecting our members from fraud is a top priority. Here’s what you need to know about these scams and how to stay safe. How the Scam Works Common Red Flags Be alert for these warning signs: How to Protect Yourself We’re Here to Help If you ever feel uncertain about a payment request or believe you’ve been targeted by a scam, contact SRI Federal Credit Union right away. Our team can help you verify the situation and take steps to protect your accounts. Fraudsters are getting more creative, but together, we can stay one step ahead. Stay informed. Stay cautious. Stay protected.
At SRI Federal Credit Union, your safety and peace of mind always come first.
Tap Cards Are Here at SRI Federal Credit Union!
Updated 02/01/2026
Big things are happening at SRI Federal Credit Union! We’re excited to announce that Tap Cards, also known as contactless payment cards, are now available for all SRIFCU Visa® Credit and Debit Cards. This means every member can now enjoy a faster, easier, and more secure checkout experience with just a simple tap. Tap Cards are a modern, more convenient way to pay. With just a quick tap on the payment terminal, you can complete purchases in seconds without swiping, inserting, or entering a PIN for most small transactions. Here’s what you can look forward to: ✅ Fast and Convenient – Tap and go at checkout counters, transit stations, vending machines, and many other places. 💳 Look for this symbol wherever you shop! Whether you’re grabbing a cup of coffee, picking up groceries, or boarding public transit, Tap Cards make everyday purchases quick and safe. If you already have an SRIFCU Visa Credit or Debit Card, your current card will automatically be replaced with a Tap Card when it expires. However, if you’d like to start tapping now, you can call us and request a Tap Card today! Tap Cards are also now available for instant issue at our branch! Tap into the future of payments with your new SRIFCU Tap Card!Why Tap Cards?
✅ Safe and Secure – Each transaction uses a unique, one-time code that helps protect you from fraud.
✅ Widely Accepted – You can use your Tap Card anywhere you see the contactless symbol:
How to Get Your Tap Card
Fraud Alert: Scammers Posing as U.S. Marshals
At SRI Federal Credit Union, protecting our members from fraud is always a top priority. We are alerting you to a new phone scam that has been reported in our community. Scammers are calling members while pretending to be U.S. Marshals or other law enforcement officials. They use intimidation tactics and claim that your accounts are “under investigation.” Victims are pressured to: Withdraw large sums of cash and tell the bank or credit union it’s for “home remodeling.” Purchase cryptocurrency, gold, or gift cards and send proof to the scammer. Hand over cash to a so-called “courier” who comes to their home. These calls are designed to create fear and urgency, making people feel they must act quickly to “protect” their money. ⚠️ Important: Real law enforcement will never call and demand money, ask you to hide the reason for a withdrawal, or send someone to your home to collect cash. If you receive one of these calls: Hang up immediately. Do not continue the conversation. Do not share personal or financial information. Verify with us directly. Call SRI Federal Credit Union at 650-800-5434 if you’re ever unsure. Report the scam. Visit ReportFraud.ftc.gov or call the National Elder Fraud Hotline at 833-372-8311. These scams often target seniors, but anyone can fall victim. Please help us spread the word by sharing this alert with family, friends, and neighbors. Together, we can stay alert, protect our finances, and stop fraud before it spreads.How the Scam Works
What You Should Do
Protect Your Community
All You Need to Know About Overpayment Scams
Great news – you’ve just received a check, and you’ve been overpaid! But there’s a catch: the check writer wants you to send the surplus back to them. Unfortunately, though, if you follow these directions, you’ll be buying right into a scam. Overpayment scams are fairly common, and for the unaware, they can be difficult to spot. Let’s take a look at these scams and what you need to know to avoid falling victim to these ruses. What is an overpayment scam? In an overpayment scam, fraudsters target an individual who’s selling a large item online, such as a car. The scammer will reach out to the seller, offering to buy their car for more than the asking price. Then, they’ll send the seller payment in the mail. At this point, the seller is thrilled. But, when the check comes, it brings with it a surprise – they’ve been overpaid. Soon after, the alleged buyer contacts the seller to ask them to refund the surplus. The seller may think it’s strange, but they comply, not wanting to keep money that isn’t theirs. The next thing they know, the original check hasn’t cleared and they realize they’ve been scammed. Not only have they not been paid for the purchase they believed the check writer was buying, but they’ve also lost the money they’ve sent back to the scammer. Red flags When selling an item on an online platform, look out for these red flags, which can alert you to a possible overpayment scam: If you encounter any of these red flags while trying to sell an item online, do not engage with the “buyer.” Block their email address and mark it as spam to avoid further contact from the scammer. You may also want to report them to the platform you’re selling the item on to help stop them from reaching out to others. How to avoid overpayment scams The FTC offers the following tips for avoiding overpayment scams when selling online: If you’ve been targeted If you believe you’ve been targeted by an overpayment scam, there are steps you can take to mitigate the damage. First, report the scam to your financial institution, as they may be able to reverse the payment. Next, alert the FTC at ftc.gov so they can do their part in catching the criminals. Finally, you can let your local law enforcement agencies know about the scam and warn your friends and family about it as well. Don’t get caught in an overpayment scam! Use this guide to stay safe.
Protecting Our Members After the NationalPublicData.com Breach
In today’s digital landscape, data breaches have become all too common. The most recent incident involves a hacker known as “USDoD,” who allegedly breached the systems of National Public Data, a company that aggregates data to provide background checks. This breach, which is believed to have started in or around April 2024, resulted in the theft of personal records that were later posted for sale and eventually released by other criminal groups onto the dark web. As a credit union committed to the security and privacy of our members, we want to keep you informed about this incident and provide you with actionable steps to protect yourself from potential fraud and account takeovers. Understanding the Breach The breach at National Public Data exposed a significant amount of personal information. While this breach did not directly involve our credit union’s systems, the compromised data could still affect our members if their personal details were included. Currently, available information suggests that this breach involved personal information—such as names, addresses, contact information, and potentially Social Security numbers—not credit or debit card information. At this time, we do not believe card data was compromised in this event. How This Could Affect You Even though credit and debit card information was not compromised, the exposure of personal data still poses a risk. Cybercriminals may use this information to engage in identity theft, phishing scams, or account takeovers. They could impersonate you, gain unauthorized access to your accounts, or create new accounts in your name. Steps to Protect Yourself Fraud Alert: A fraud alert is a warning placed on your credit report that tells creditors to take extra steps to verify your identity before issuing credit in your name. This can be particularly helpful if you believe your personal information may have been compromised, as it makes it harder for identity thieves to open new accounts. How to Place a Fraud Alert: Credit Freeze: A credit freeze (also known as a security freeze) is a more robust protection that locks your credit report, preventing creditors from accessing it entirely. This means that new credit accounts cannot be opened in your name while the freeze is in place. Unlike a fraud alert, a credit freeze does not expire and remains in place until you remove it. How to Place a Credit Freeze: Our Commitment to Your Security At SRI Federal Credit Union, your security is our top priority. We are continuously monitoring our systems and taking proactive measures to protect your accounts. We also encourage you to take these precautions to safeguard your personal information. If you have any questions or concerns, please do not hesitate to reach out to our member services team. Together, we can protect your financial well-being and maintain the trust you’ve placed in us.
All You Need to Know About One-Time Password Scams
One-time passwords (OTPs) are a crucial security feature in our digital age by offering an extra layer of protection for online transactions and account logins. Unfortunately, though, scammers often try to hijack these codes to steal sensitive information, money, or both. Here’s what you need to know about one-time password scams and how to avoid them. What is a one-time password scam? One-time password (OTP) scams are designed to trick individuals into sharing their OTPs, which scammers then use to gain unauthorized access to accounts. Here are the various ways these scams go down: Whichever method is deployed in an attempt to steal your OTP, the scammer will then use it to access your accounts and possibly steal your identity Red flags Avoid falling victim to a one-time password scam by watching out for these red flags: Protect yourself Staying safe from OTP scams requires vigilance and adopting best practices for online security. Here are some steps you can take: If you’ve been targeted If you believe you’ve been scammed and/or have shared your OTP, take immediate action. First, change the passwords on all affected accounts and those that have similar login credentials. Next, inform the host organization of the account that it’s been compromised. They can help secure your account and guide you on additional steps to take. Monitor your accounts in the ensuing weeks and months, keeping a close eye on your financial statements and account activity for any unauthorized transactions. Finally, file a report with your local consumer protection agency, the Federal Trade Commission (FTC), and the Internet Crime Complaint Center (IC3). You may also want to consider identity theft protection at this time if sensitive information was compromised. One-time password scams can be difficult to spot and wreak massive damage. Use this guide to learn about one-time password scams and how to prevent yourself from falling victim. Stay safe!